Discover ByRATINGS
Predictive Marketing for success
Predict the behaviour of your customers to optimise your Acquisition, Engagement, Conversion and Retention strategies.
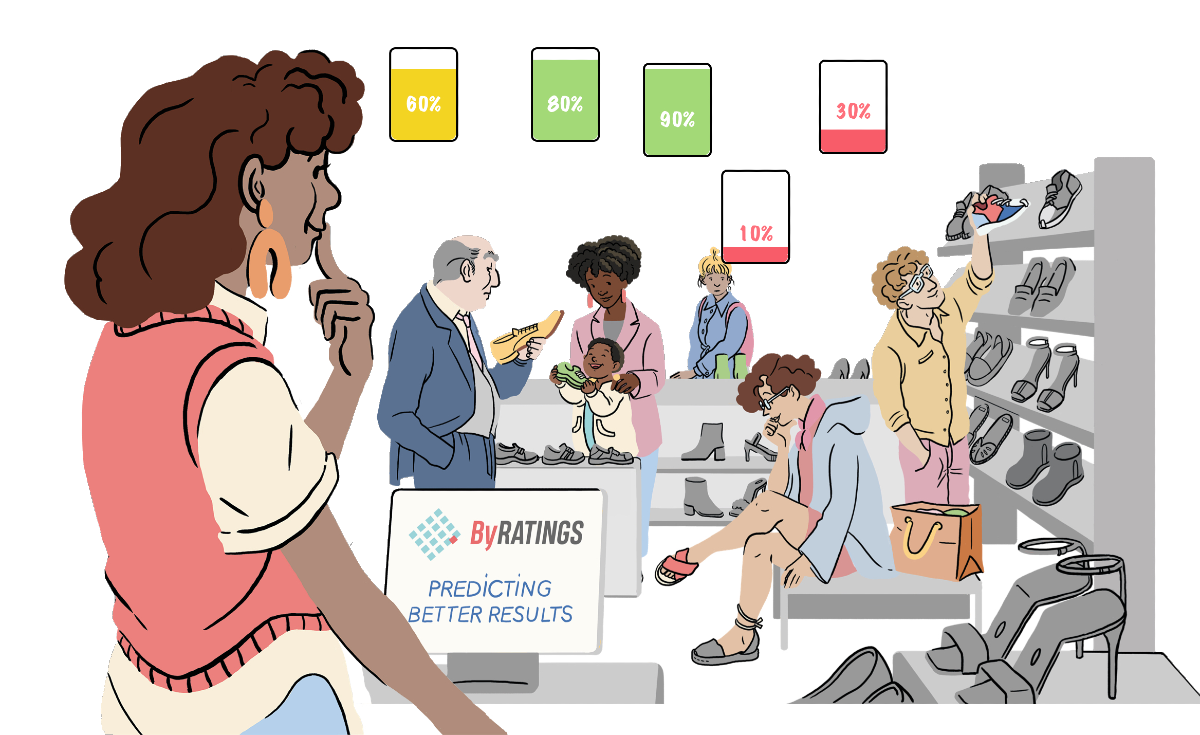
ByRATINGS incorporates Predictive Marketing throughout the sales funnel to optimize both the KPIs of Marketing teams and the ROI of sales teams. ByRATINGS products are designed to solve specific problems in your industry.
At ByRATINGS we develop custom Machine Learning and Deep Learning algorithms to help you get the best out of your data. By predicting your customers’ behaviour, you can optimise your strategies and achieve better results.
Predictive funnel
Convert your sales funnel into a predictive funnel by applying innovative and high-performance AI solutions.
Seamless integration
We offer you scalable solutions that are easy to integrate through our connectors.
Improved Results
Predictive Marketing allows you to understand your customers and know what they really need.
Since
2014
APPLYING PREDICTIVE MARKETING
Over
1000
ALGORITHMS DEVELOPED
Over
250
PROJECTS IN DIFFERENT SECTORS
Over
2,5M
PREDICTIONS PER MONTH
Over
20+
INTEGRATION CONNECTORS
UNLOCK THE POWER OF YOUR DATA
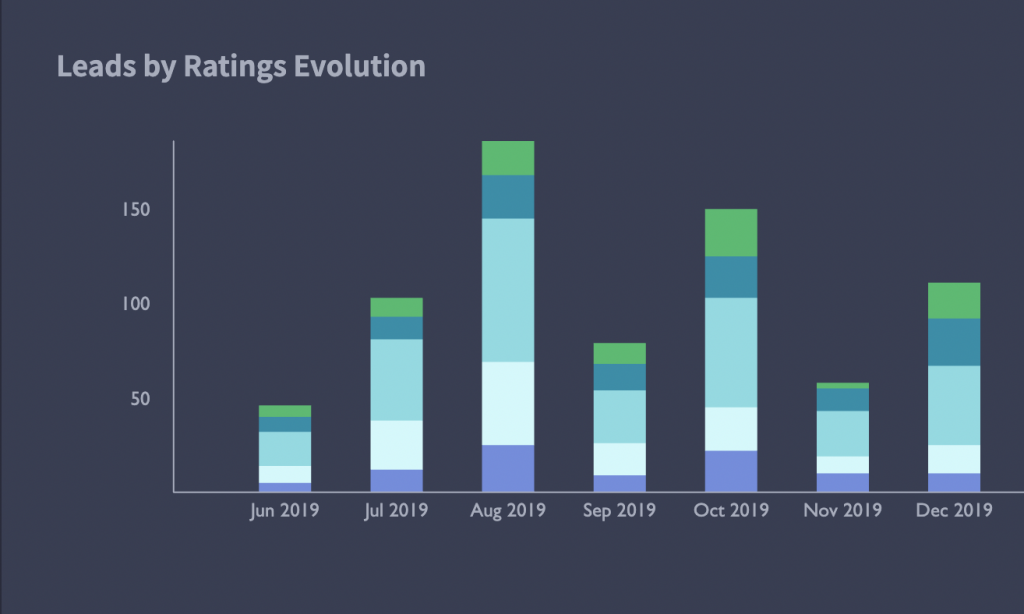
A powerful and easy-to-use predictive dashboard
The ByRATINGS Dashboard allows you to integrate predictability into the analysis of all your marketing and sales KPIs.
Real-Time Prediction
Visualise and analyse your customers’ behaviour in real time.
Multiple Views
Analyse your customers’ behaviour by profile, source, product and much more.
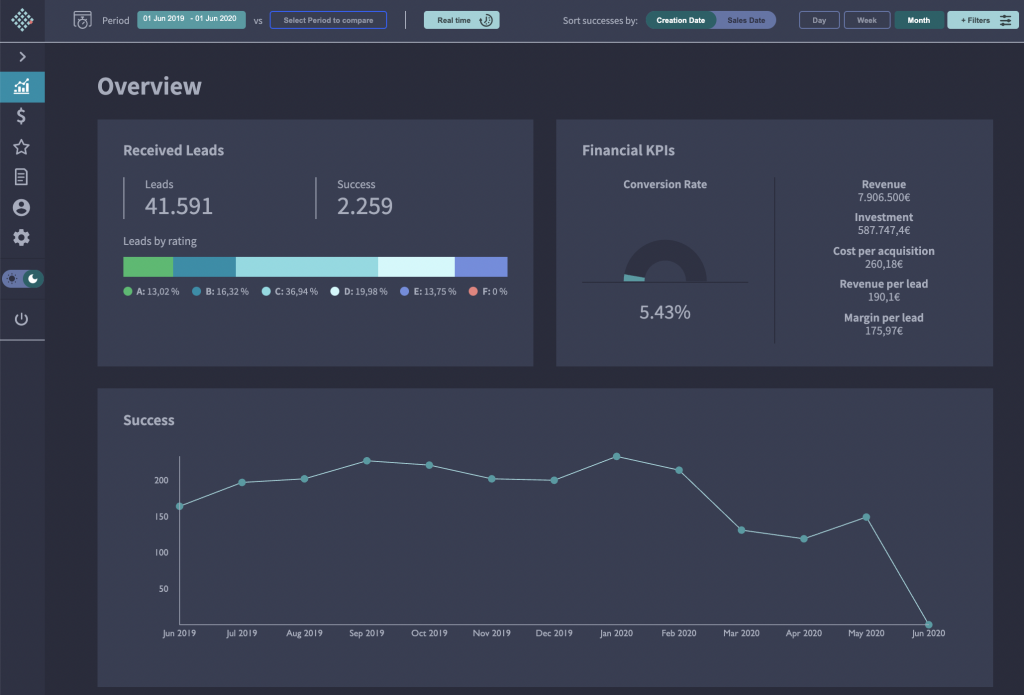
Financial KPIs
Predict the profitability of your campaigns and create a more accurate sales forecast.
Easy to Use
Integrate and customise in just one click.
RESULTS BASED ON CUSTOM SOLUTIONS
Companies that have trusted ByRATINGS share their experiences and results.


“ByRatings is a must-have if you generate a large volume of leads. It increases efficiency, helps to prioritise what is important and it does it better every day. Its success rate is unbelievable”
Luis Encabo, Global head of sales B2C
Challenge
ThePowerMBA requires a lead prioritisation tool to be able to manage the large amount of users interested in the course.
Solution
To sustain its level of growth, ThePowerMBA needed an efficient and scalable lead qualification model.



Got a new challenge for us?
Find out how our predictive marketing solutions can optimise your results.
Solutions
Integrations
Company
© ByRatings 2021





 Español
Español